What makes it whitebox
Traditional automated scanners probe your application from the outside. Mjolnir starts from the inside, reading your source code to understand your routes, authentication flows, data models, and business logic before it ever sends a single request. This means it finds vulnerabilities that black-box tools miss: logic flaws, broken access controls, misconfigured authorization chains, and authentication bypasses that only make sense once you understand the code behind them.How a run works
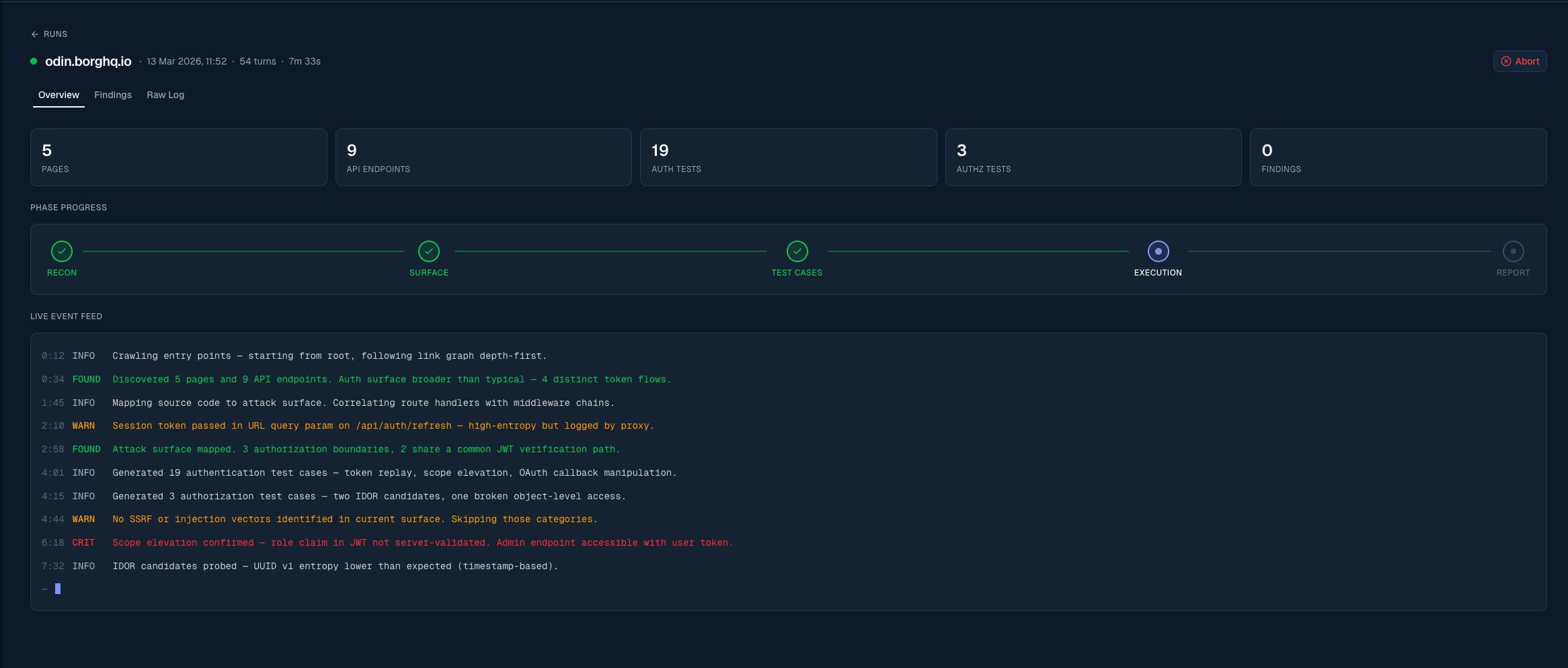
Reconnaissance
Mjolnir crawls your application and cross-references what it finds with your source code to build a complete picture of the attack surface.
Attack surface mapping
Routes, endpoints, middleware chains, authentication boundaries, and data flows are mapped and catalogued.
Test case generation
Based on the attack surface, Mjolnir generates targeted test cases for each vulnerability category: authentication, authorization, injection, and more.
Execution
Test cases are executed against your target URLs using your provided test users and credentials.
What Mjolnir tests for
Mjolnir generates test cases across a broad range of vulnerability categories, including:Authentication
Login bypasses, weak credential policies, session fixation, token leakage, and insecure password reset flows.
Authorization
Privilege escalation (vertical and horizontal), broken access controls, IDOR, and missing function-level checks.
Injection
SQL injection, NoSQL injection, command injection, SSTI, and other server-side injection vectors.
Data exposure
Sensitive data in responses, overly permissive API fields, PII leaks, and missing data redaction.
No-cure, no-pay
If Mjolnir doesn’t find any vulnerabilities, you don’t pay. Simple as that. Your Borg subscription covers the full Odin platform: continuous asset discovery, findings management, issue tracker integration, and reporting. The Mjolnir pentest minutes are part of a broader platform designed to improve your security posture over time.Setting up a run
A Mjolnir run is configured through a five-step wizard:| Step | What you do |
|---|---|
| 1. Connect GitHub | Grant Mjolnir read access to your repositories |
| 2. Scope & Connectivity | Define target URLs and verify Mjolnir can reach them |
| 3. Test Users | Add authenticated test accounts for role and tenant testing |
| 4. Code & Documentation | Select repos and upload supporting files |
| 5. Review & Verify Domain | Review configuration and prove domain ownership |
Start setup: Connect GitHub
Begin the Mjolnir setup wizard